The new CMMC data protection security requirements from the U.S. Department of Defense (DoD) will have an enormous impact on commercial companies doing business with the DoD. By 2026, any commercial company that wants to bid on a DoD contract will be required to be CMMC certified. Gartner estimates over 350,000 vendors will be impacted by CMMC.
Most organizations are just starting to prepare for a CMMC certification, and their activities are focused on two areas of preparation:
1. Education & Awareness
2. Self Assessment
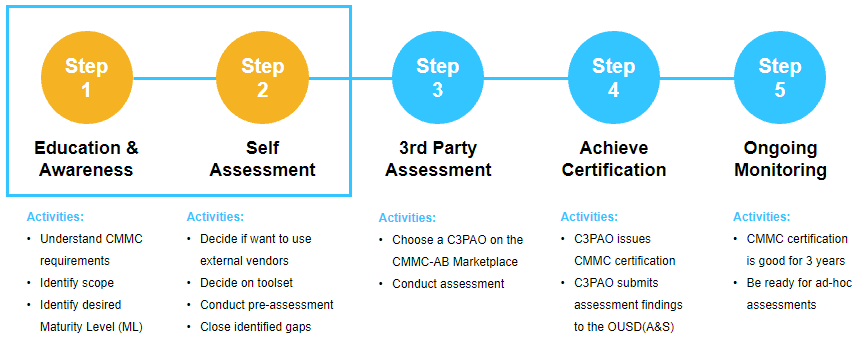
The education step involves understanding the CMMC requirements, identifying the scope of the assessment, and identifying which CMMC level of certification is needed.
Next, the organization will begin the self assessment. This is the best way to prepare for the certification assessment by a CMMC Third-Party Assessor Organization (C3PAO). It will help the organization identify the gaps and deficiencies that would cause them to fail the assessment. And most importantly, this forces the organization to go through all the Assessment Objectives that must be answered when the C3PAO shows up to do the real assessment – there are hundreds of these Assessment Objectives!
This is why Archer created the new Archer CMMC Management use case. It is specifically designed to help organizations get ready for a CMMC assessment. Archer worked closely with CMMC experts and Department of Defense insiders to understand what a C3PAO would be looking for when conducting the assessment to make sure the use case provides exactly what is needed to pass a CMMC certification assessment.
Archer CMMC Management enables organizations to:
- Identify, document, and manage the appropriate CMMC practices and processes required for improved cybersecurity hygiene for storage and management of controlled unclassified information (CUI).
- Manage pre-assessment activities such as defining scoped boundaries, system components, policies, and procedures.
- Allocate the appropriate assessment processes, assessment practices, and assessment objectives across the different components of the system.
- Identify and track deficiencies and remediate plans of action and milestones (POA&Ms).
- Create the appropriate system security plan (SSP) documentation.
Interested in learning more about Archer CMMC Management? Join us for a Free Friday Tech Huddle on Friday, November 12 for a live demo. Free Friday Tech Huddles are only available to Archer customers. If you are not yet a customer but you are interested in learning more, please contact your local representative or authorized reseller — or visit us at www.archerirm.com.