Warren Buffett recently sent out biennial letter to Berkshire Hathaway managers re-emphasizing the top priority “we can afford to lose money – even a lot of money. But we can’t afford to lose reputation – even a shred of reputation”. This is a powerful statement & goes to the heart of managing a business.
Given the security landscape today, reputation is at risk not just from bad governance in the company, but also from how the security is managed so adversaries are kept at bay.
Picture this: a global organization, with thousands of employees, billions of dollars in revenue and a stellar reputation. The IT team is tasked to get a good handle on managing the ever growing pile of vulnerabilities. This is a big pile of unknown risk that needs to be addressed.
Since the IT team understands the problem well, they decide to create a homegrown solution figuring it will be easy to customize and they can then shape the solution based on the unique business requirements. The team then builds a case for quick return on investment and wins go-ahead.
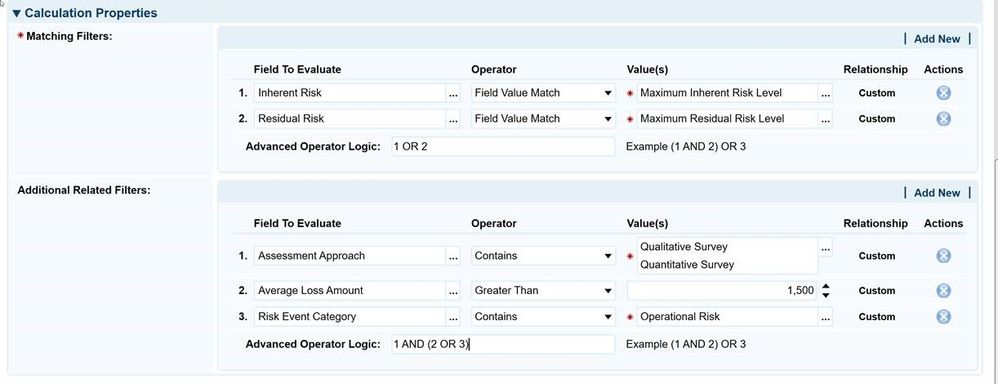
As the team embarks on this journey, they start to feel some of the challenges. The first step is to nail down the requirements then build the solution. However, the requirements seem to be a never ending stream. As they get close to finishing the solution they get the feeling that building the solution was probably the easy part.
This is when they begin to realize that the solution may not be sustainable!
Some of the challenges they run into –
- Full time resources are required to continue to enhance & maintain the solution.
- The brightest resources are taken away from security tasks and are dedicated to managing the solution.
- Functionality is limited. As an example, cannot identify unique assets since the algorithm is based off IP addresses as primary keys, which leads to assets with overlapping IP addresses.
- Can’t get away from using Sharepoint in some form or the other.
- Reports are still generated manually and not consistent quarter-over-quarter.
From a business perspective, what does this lead to?
- More resources are required for managing vulnerabilities.
- Lack of resources push some of the required activities such as penetration testing into corner.
- Unaddressed vulnerabilities are still rising. Rapid remediation validation is not happening leading to closing of vulnerabilities that have not been remediated.
- Tracking of vulnerability is quite tedious. Business line managers are unable to see where their requests are in review & approval process.
- The IT team is limited in the metrics & KPIs (key performance indicators) they can create for the vulnerability management process.
You can be proactive and avoid these negative business outcomes.
In the end you are looking to guard the reputation of the business. Managing security in the right way can yield a significant competitive advantage by protecting the reputation of business in the long run. Do it the right way.
-
Stay in touch @RajMeel7