Use Case Announcements
Read and subscribe to the latest announcements for Archer Us...
Important Update: Community URLs redirect issues are partially resolved. Learn More. .

Read and subscribe to the latest announcements for Archer Us...
Access documentation for Archer Use Cases
Learn more about Archer Solutions and Use Cases
View short demonstrations of Archer use cases
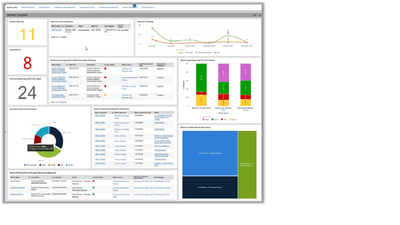
Demonstration For More Information Archer Insight Overview To learn more about how Archer products, services, and solutions can help solve your business and IT challenges, contact your local representative or authorized reseller—or visit us at www.ar...
CMMC Management Preparing for a CMMC assessment is a new and significant challenge for organizations seeking certification. To meet the challenges of CMMC certification, Archer CMMC Management enables organizations to identify, document, and manage t...

Information Security Management System (ISMS) Archer Information Security Management System (ISMS) allows you to quickly scope your information security management system (ISMS) and document your Statement of Applicability for reporting and certifica...

IT Regulatory Management Archer IT Regulatory Management provides organizations with the necessary tools and capabilities to document external regulatory obligations. Organizations can establish a systematic review and approval process for tracking c...

Cyber Incident & Breach Response Archer Cyber Incident & Breach Response enables you to centrally catalog organizational and IT assets, establishing business context to drive incident prioritization and implement processes designed to escalate, inves...

PCI Management Archer PCI Management enables organizations to streamline the compliance process, simplify stakeholder participation, and reduce overall compliance effort and cost. It allows organizations to jumpstart a PCI compliance program by condu...

IT Risk Management Archer IT Risk Management enables you to comprehensively catalog organizational hierarchies and IT assets to ensure all business critical connections are documented and understood in the proper context of IT risk management. This u...

IT Security Vulnerabilities Program Archer IT Security Vulnerabilities Program enables security teams to systematically identify and prioritize threats and vulnerabilities based on the risk level to the business. Proactively manage IT security risks ...

IT Controls Assurance Archer IT Controls Assurance provides the ability to take a project-based approach to controls testing and assess and report on the performance of controls across all IT assets and automate control assessment and monitoring. Wit...

IT & Security Policy Program Management Archer IT & Security Policy Program Management provides the framework for establishing a scalable and flexible environment to manage corporate and regulatory policies and ensure alignment with compliance obliga...

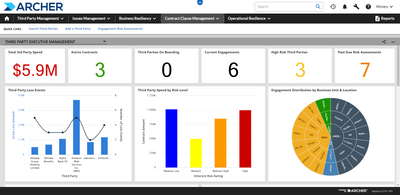
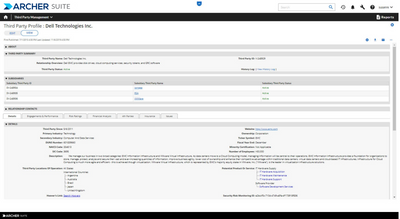
Archer Third Party Governance automates and streamlines oversight of vendor relationships. The solution facilitates key activities necessary to fulfill regulatory obligations and best practices across the entire third party management lifecycle as pa...

Third Party Governance The Archer® Third Party Governance use case provides supplier engagement performance monitoring. Metrics can be established within four categories: Quality, Innovation, Performance, and Relationship. Metrics are depicted for ea...

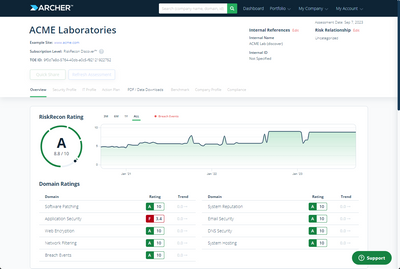
Third Party Security Risk Monitoring Archer® Third Party Security Risk Monitoring delivers transparent security measurements, analytics, and analyst-level insight to dramatically improve your third-party information security risk management program. ...

Third Party Engagement Archer® Third Party Engagement allows you to catalog the products and services being delivered to your organization by third parties. It also allows you to associate product and service engagements to the business process and b...

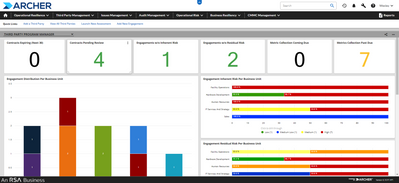
Third Party Risk Management Archer® Third Party Risk Management employs a series of risk assessment questionnaires for third parties, enabling your organization to assess their internal controls and collect relevant supporting documentation for furth...

Third Party Catalog Archer® Third Party Catalog allows you to document all third-party relationships, engagements , and associated contracts, as well as the business units and named individuals in your organization that are responsible for each third...

Crisis Management Archer® Crisis Management provides a coordinated, consistent and automated approach to handling crisis events. By aligning crisis management with incident response, you can respond earlier to incidents and in crisis situations to pr...

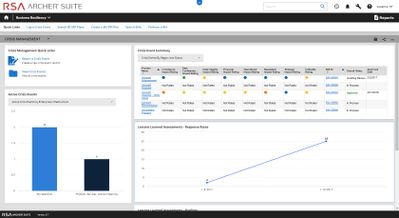
Incident Management Archer Incident Management provides case management and incident response for reporting and categorizing cyber and physical incidents and determining the appropriate response procedures. The use case allows you to evaluate the cri...

Business Impact Analysis Archer Business Impact Analysis helps you determine the criticality of your products and services, business processes and supporting infrastructure so you can make the most important of these resilient to disruption. It creat...

Archer® Business Continuity & IT Disaster Recovery Planning enables you to perform risk assessments and document and test business continuity and IT disaster recovery plans that target your organization, including business processes, locations, IT ap...
