Why Archer is combining Business Resiliency and Operational Resilience Solutions
Read more about why Archer is combining Business Resiliency and Operational Resilience Solutions
Important Update: Community URLs redirect issues are partially resolved. Learn More. .
Read more about why Archer is combining Business Resiliency and Operational Resilience Solutions
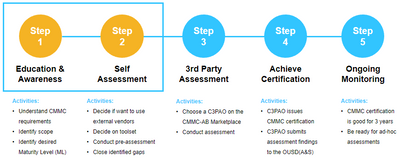
The new CMMC data protection security requirements from the U.S. Department of Defense (DoD) will have an enormous impact on commercial companies doing business with the DoD. By 2026, any commercial company that wants to bid on a DoD contract will be...
Even the slightest bit of resistance can get in the way in completing a key risk process. If a form is hard to figure out or cumbersome to navigate, users will avoid it, putting it off until the last minute or forgetting about it completely. That res...


Self-Troubleshooting is a digital, fully automated solution that empowers Archer customers to auto resolve support requests, without human intervention and at a 99.9% enhanced time to resolve… 2-3 min. vs 2-3 days. In addition, it allows customers – ...
With data breaches increasing at a record pace, an Information Security Management System (ISMS) has transformed from an IT buzzword into a necessity for most organizations. According to a report recently released by the Identify Theft Resource Cente...


The RSA Archer Suite includes 36 multi-disciplinary risk management use cases across 7 solutions areas that address the most critical areas of business risk. Each use case comes with a Use Case Guide, which will get you started with overview and desi...
Do you ever use the term, ‘you are creating a tempest in a teapot’? It means, don’t make a big deal out of something that isn’t. Doing a little research, I found other similar phrases I thought were entertaining. They are: 'A storm in a teacup' – Cic...

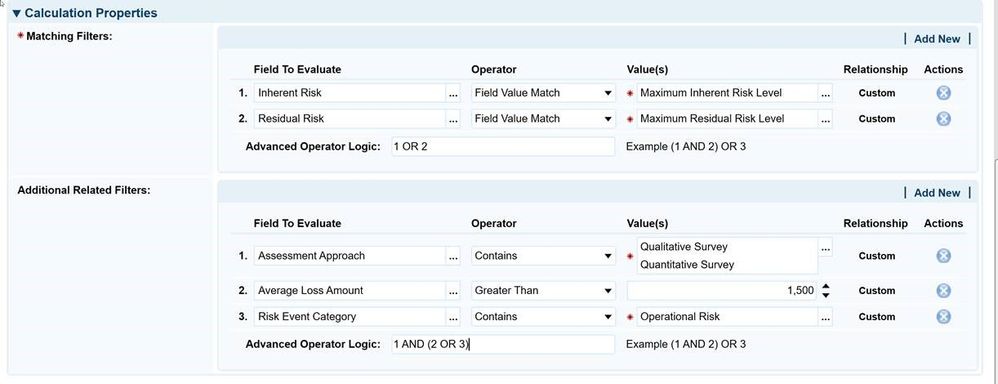
Organizations must implement a cohesive risk management program to protect against loss while remaining agile to meet strategic objectives. RSA Archer® can transform your compliance program and enable your organization to proactively manage risk by p...
The Defend the Kingdom blog series is a fictional storyline following the adventures of Marty Bishop, a skilled, imaginative security administrator fighting cybercrime on the frontlines of the massive multi-national conglomerate MagnaCorp. Starting a...

This integration guide provides information on collecting RSA Archer accounts, groups and roles details and using the RSA IMG solution to report, review and request access. The supported platform versions for this capability are as follows: RSA Arche...
You know the age old joke right? Suppliers, vendors, or third parties as they are commonly known, have become an integral part of business operations for most organizations. Wal-Mart utilizes over 60,000 of them, while Boeing has over 21,000. Know ho...
Final installation of Continuous Monitoring white paper series. Part 3 covers "Managing Assessment Costs". CM has the potential to explode your IA budget. Learn how to lessen that impact.
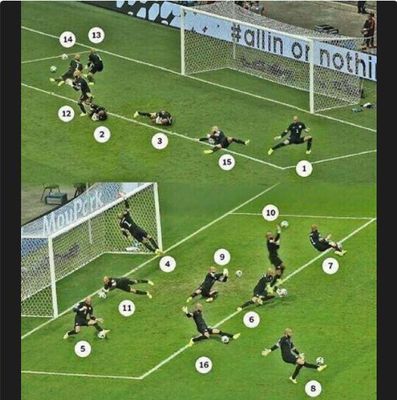
Whether you're a World Cup 2014 soccer fan or not, you've probably heard about Tim Howard, the goalie for Team USA. Tim had an unbelievable performance during Team USA's run through the World Cup tournament, but especially against Team Belgium, where...